k-vid.net
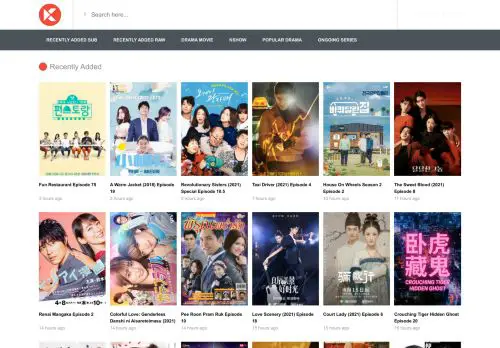
K-vid : Watch Korea videos from everywhere: K-vid : Watch Korea videos from everywhere.
k-vid.net is a safe website about "K-vid : Watch Korea videos from everywhere" in ago category. The server is running at 104.21.7.212 ip address and there is no secure connection certificate between the website and the visitor. When we did a security search, no viruses or spam were detected on web page. K-vid have daily 2K and monthly 62K unique visitors from Cambodia and Sri Lanka. According to our financial situation analysis, this website earns an estimated daily $9, weekly $40 and monthly $277 from online advertising. If you want to buy this domain, you need to revise $1814. Because the value of the website can range from at least $1260 to $2367.
- Daily Visitor
2K - Daily Revenue
$9 - Monthly Visitor
62K - Monthly Revenue
$277
User Reviews k-vid.net
Please write your , and overall score.
k-vid Server Status
| Date | Server Status | Speed |
|---|---|---|
| 2024-04-02 06:54:12 | Up | 1.392 Second |
| 2024-04-01 20:08:12 | Up | 1.161 Second |
| 2024-04-01 09:22:10 | Up | 1.323 Second |
| 2024-03-31 22:36:11 | Up | 6.265 Second |
| 2024-03-31 11:50:11 | Up | 8.043 Second |
| 2024-03-30 04:54:09 | Up | 2.314 Second |
| 2024-03-29 18:08:09 | Up | 1.280 Second |
| 2024-03-29 07:22:10 | Up | 6.170 Second |
| 2024-03-28 20:36:09 | Up | 6.171 Second |
| 2024-03-28 09:50:12 | Up | 7.847 Second |
| 2024-03-27 23:04:09 | Up | 1.251 Second |
| 2024-03-27 12:18:12 | Up | 6.102 Second |
| 2024-03-27 01:32:09 | Up | 1.121 Second |
| 2024-03-26 14:46:12 | Up | 1.019 Second |
| 2024-03-26 04:00:12 | Down | 9.999 Second |
| 2024-03-25 17:12:12 | Up | 1.550 Second |
| 2024-03-25 14:08:35 | Up | 8.173 Second |
| 2024-03-25 11:58:36 | Up | 15.46 Second |
| 2024-03-25 09:48:34 | Up | 8.575 Second |
| 2024-03-25 07:38:33 | Up | 1.079 Second |
Known Searchs
-wwkodoku no gourmet season 7
☁ Content Metrics
- ago 10%
- episode 10%
- 2021 7%
- hours 5%
- day 4%
- love 1%
- the 1%
- season 1%
- drama 1%
- recently 1%
- added 1%
- special 1%
- ruk 1%
- korea 1%
- won 0%
- top 0%
- king 0%
- chef 0%
- 2015 0%
- 270 0%
- %
Website raw article content tells search engines what your web page content is about. The word usage rate is very important and the frequency of words used above 4% is perceived as spam.
☯ Technology Analysis
- - Cookie - PHP - cloudflare - CloudFlare
☂ Security Analytics
- ✔ CMC Threat Intelligence
- ✔ CLEAN MX
- ✔ DNS8
- ✔ Cisco Talos IP Blacklist
- ✔ Web Security Guard
- ✔ VX Vault
- ✔ Baidu-International
- ✔ Netcraft
- ✔ Armis
- ✔ BADWARE.INFO
- ✔ MalBeacon
- ✔ Comodo Valkyrie Verdict
- ✔ PhishLabs
- ✔ EmergingThreats
- ✔ Forcepoint ThreatSeeker
- ✔ Sangfor
- ✔ K7AntiVirus
- ✔ SecureBrain
- ✔ Virusdie External Site Scan
- ✔ Artists Against 419
- ✔ CINS Army
- ✔ Cyren
- ✔ Quttera
- ✔ AegisLab WebGuard
- ✔ MalwareDomainList
- ✔ Lumu
- ✔ Google Safebrowsing
- ✔ Kaspersky
- ✔ BitDefender
- ✔ GreenSnow
- ✔ G-Data
- ✔ AlienVault
- ✔ CyberCrime
- ✔ Malware Domain Blocklist
- ✔ MalwarePatrol
- ✔ Fortinet
- ✔ Feodo Tracker
- ✔ AICC (MONITORAPP)
- ✔ CyRadar
- ✔ desenmascara.me
- ✔ ADMINUSLabs
- ✔ IPsum
- ✔ Dr.Web
- ✔ Cyan
- ✔ Emsisoft
- ✔ Rising
- ✔ Spamhaus
- ✔ malwares.com URL checker
- ✔ Phishtank
- ✔ EonScope
- ✔ Malwared
- ✔ Avira
- ✔ NotMining
- ✔ securolytics
- ✔ Antiy-AVL
- ✔ SCUMWARE.org
- ✔ Trustwave
- ✔ Certego
- ✔ Yandex Safebrowsing
- ✔ ESET
- ✔ Threatsourcing
- ✔ URLhaus
- ✔ MalSilo
- ✔ Nucleon
- ✔ PREBYTES
- ✔ Sophos
- ✔ Blueliv
- ✔ BlockList
- ✔ Hoplite Industries
- ✔ AutoShun
- ✔ ThreatHive
- ✔ CRDF
- ✔ FraudScore
- ✔ Quick Heal
- ✔ Tencent
- ✔ OpenPhish
- ✔ StopBadware
- ✔ Sucuri SiteCheck
- ✔ zvelo
- ✔ StopForumSpam
- ✔ ZeroCERT
- ✔ Spam404
- ✔ Phishing Database
- ✔ alphaMountain.ai
✇ DNS Records
| Record | Class | TTL | Value |
|---|---|---|---|
| A | IN | 299 | ip: 172.67.188.9 |
| A | IN | 299 | ip: 104.21.7.212 |
| NS | IN | 21599 | target: kate.ns.cloudflare.com |
| NS | IN | 21599 | target: tim.ns.cloudflare.com |
| SOA | IN | 3600 | mname: kate.ns.cloudflare.com rname: dns.cloudflare.com serial: 2036544048 refresh: 10000 retry: 2400 expire: 604800 minimum-ttl: 3600 |
| AAAA | IN | 300 | ipv6: 2606:4700:3030::6815:7d4 |
| AAAA | IN | 300 | ipv6: 2606:4700:3030::ac43:bc09 |
ℹ Whois Data
Domain Name: K-VID.NET
Registry Domain ID: 2079563351_DOMAIN_NET-VRSN
Registrar WHOIS Server: whois.namecheap.com
Registrar URL: http://www.namecheap.com
Updated Date: 2020-12-06T07:20:08Z
Creation Date: 2016-12-06T06:29:11Z
Registry Expiry Date: 2021-12-06T06:29:11Z
Registrar: NameCheap, Inc.
Registrar IANA ID: 1068
Registrar Abuse Contact Email: abuse@namecheap.com
Registrar Abuse Contact Phone: +1.6613102107
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Name Server: KATE.NS.CLOUDFLARE.COM
Name Server: TIM.NS.CLOUDFLARE.COM
DNSSEC: unsigned
URL of the ICANN Whois Inaccuracy Complaint Form: https://www.icann.org/wicf/
>>> Last update of whois database: 2021-04-18T07:05:39Z <<<
✉ Host Network Data
#
# ARIN WHOIS data and services are subject to the Terms of Use
# available at: https://www.arin.net/resources/registry/whois/tou/
#
# If you see inaccuracies in the results, please report at
# https://www.arin.net/resources/registry/whois/inaccuracy_reporting/
#
# Copyright 1997-2021, American Registry for Internet Numbers, Ltd.
#
#
# Query terms are ambiguous. The query is assumed to be:
# "n 172.67.188.9"
#
# Use "?" to get help.
#
NetRange: 172.64.0.0 - 172.71.255.255
CIDR: 172.64.0.0/13
NetName: CLOUDFLARENET
NetHandle: NET-172-64-0-0-1
Parent: NET172 (NET-172-0-0-0-0)
NetType: Direct Assignment
OriginAS: AS13335
Organization: Cloudflare, Inc. (CLOUD14)
RegDate: 2015-02-25
Updated: 2017-02-17
Comment: All Cloudflare abuse reporting can be done via https://www.cloudflare.com/abuse
Ref: https://rdap.arin.net/registry/ip/172.64.0.0
OrgName: Cloudflare, Inc.
OrgId: CLOUD14
Address: 101 Townsend Street
City: San Francisco
StateProv: CA
PostalCode: 94107
Country: US
RegDate: 2010-07-09
Updated: 2021-01-11
Ref: https://rdap.arin.net/registry/entity/CLOUD14
OrgAbuseHandle: ABUSE2916-ARIN
OrgAbuseName: Abuse
OrgAbusePhone: +1-650-319-8930
OrgAbuseEmail: abuse@cloudflare.com
OrgAbuseRef: https://rdap.arin.net/registry/entity/ABUSE2916-ARIN
OrgNOCHandle: NOC11962-ARIN
OrgNOCName: NOC
OrgNOCPhone: +1-650-319-8930
OrgNOCEmail: noc@cloudflare.com
OrgNOCRef: https://rdap.arin.net/registry/entity/NOC11962-ARIN
OrgTechHandle: ADMIN2521-ARIN
OrgTechName: Admin
OrgTechPhone: +1-650-319-8930
OrgTechEmail: rir@cloudflare.com
OrgTechRef: https://rdap.arin.net/registry/entity/ADMIN2521-ARIN
RTechHandle: ADMIN2521-ARIN
RTechName: Admin
RTechPhone: +1-650-319-8930
RTechEmail: rir@cloudflare.com
RTechRef: https://rdap.arin.net/registry/entity/ADMIN2521-ARIN
RAbuseHandle: ABUSE2916-ARIN
RAbuseName: Abuse
RAbusePhone: +1-650-319-8930
RAbuseEmail: abuse@cloudflare.com
RAbuseRef: https://rdap.arin.net/registry/entity/ABUSE2916-ARIN
RNOCHandle: NOC11962-ARIN
RNOCName: NOC
RNOCPhone: +1-650-319-8930
RNOCEmail: noc@cloudflare.com
RNOCRef: https://rdap.arin.net/registry/entity/NOC11962-ARIN
#
# ARIN WHOIS data and services are subject to the Terms of Use
# available at: https://www.arin.net/resources/registry/whois/tou/
#
# If you see inaccuracies in the results, please report at
# https://www.arin.net/resources/registry/whois/inaccuracy_reporting/
#
# Copyright 1997-2021, American Registry for Internet Numbers, Ltd.
#
☰ HTTP Header
| date | sun, 18 apr 2021 07 |
|---|---|
| content-type | text/html; charset=utf-8 |
| transfer-encoding | chunked |
| connection | keep-alive |
| set-cookie | __cfduid=dd964691a27fd00383255d14ff2770ed01618729548; expires=tue, 18-may-21 07 |
| vary | accept-encoding |
| vary | accept-encoding |
| x-powered-by | php/5.6.13 |
| set-cookie | tvshow=lbvtbje6f10bsgnh0shtvftd97; path=/ |
| expires | thu, 19 nov 1981 08 |
| cache-control | no-store, no-cache, must-revalidate, post-check=0, pre-check=0 |
| pragma | no-cache |
| set-cookie | token=607bda4c64187; path=/ |
| cf-cache-status | dynamic |
| cf-request-id | 098565d2150000d25486a56000000001 |
| report-to | {"endpoints" |
| nel | {"report_to" |
| server | cloudflare |
| cf-ray | 641c0bfceffed254-sof |
| content-encoding | gzip |
| alt-svc | h3-27=" |
✔ Robots.txt File
User-agent: *
Disallow: /user/